Articles tagged with "Training"
 Credit: Patrick Tomasso @ Unsplash
Credit: Patrick Tomasso @ Unsplash
AppSec Strategy for AWS Cloud SaaS
The purpose of this document is to outline an application security strategy and roadmap for AWS Cloud SaaS applications, covering both application security concerns as well as AWS specific infrastructure. This is a checklist style article to help start conversations and give you information to perform further research. I’ve referenced other white papers and further reading available for more information throughout. An effective application security program will reduce security risk associated with code development while keeping disruption to the normal SDLC processes to a minimum. Ideally, this is done in an environment that fosters cooperation and transparency between AppSec professionals and the development team as a whole. If the entirety of the team is on the same page in regard to application security goals, and the maturity journey to get there, then the security team can operate as a service organization whose goal is enablement, rather than as a policing organization whose goal is governance.Purpose
Application Security
Read more >>
 Credit: Daniel McCullough @ Unsplash
Credit: Daniel McCullough @ Unsplash
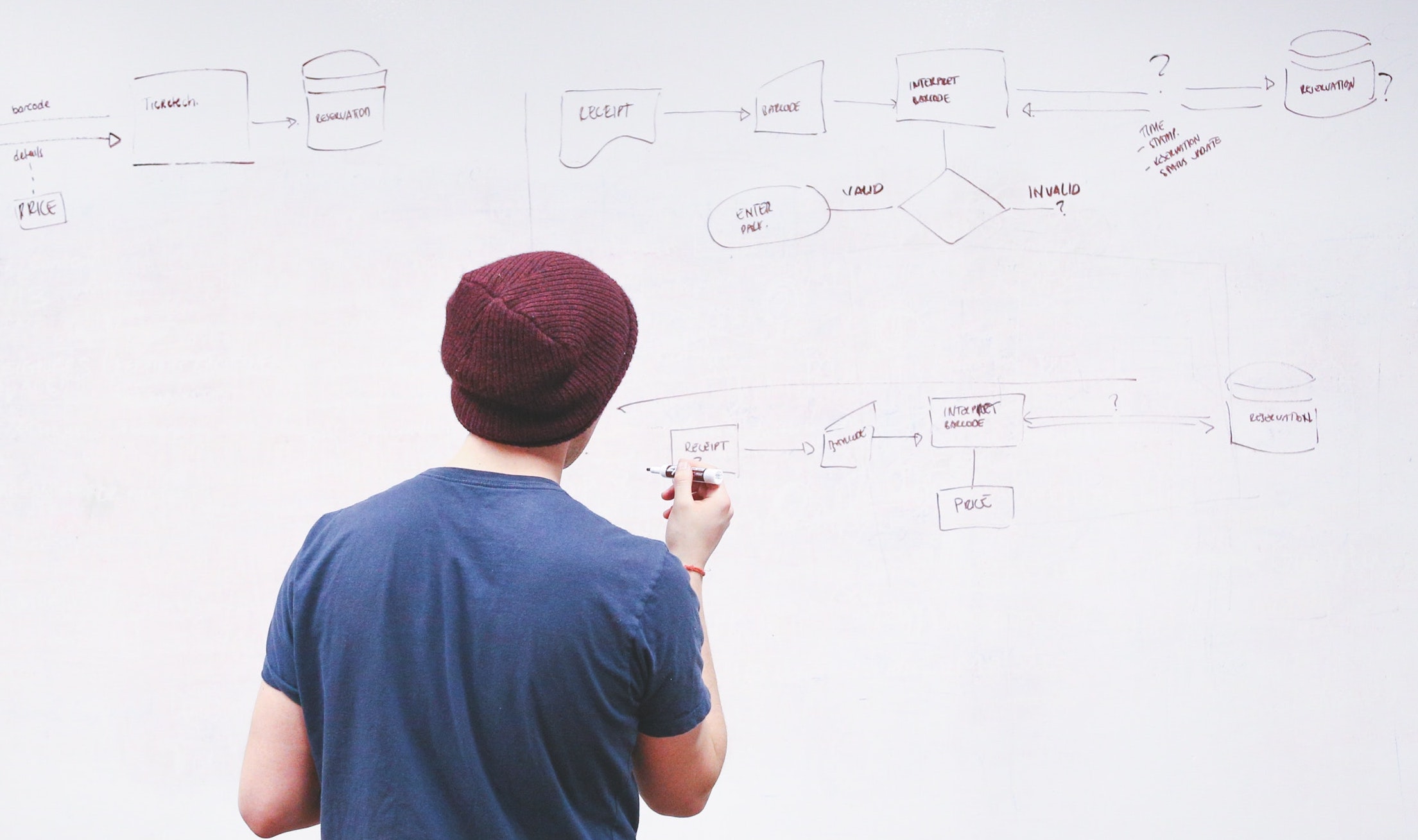
System Design for Security
My background is as a developer and a security professional, so when I had to learn system design I approached it from that perspective. While I was familiar with many of these concepts, I decided that I had to learn it in depth and in earnest. Now that I know more, I’m convinced that every developer and every security professional should understand these concepts. For all of you who are like me and want to learn more, here’s an overview to help you think about system design, coming at it from a mindset of application security.
Read more >>
 Credit: Barry Weatherall @ Unsplash
Credit: Barry Weatherall @ Unsplash
AppSec Vulnerability Cheatsheet
There are a number of places online where you can find details about application security vulnerabilities, but it is surprisingly hard to find a single location that provides a summary of all the most important vulnerabilities to be aware of. While any high-risk vulnerability is worth fixing, It’s worth adding a layer of prioritization around the most common vulnerabilities that are being used in attacks and exploits. The following statistics were reported by Contrast Security. While this is based primarily on what they are seeing with their customers, I think it is generally useful:
Read more >>
 Credit: Joe Basirico
Credit: Joe Basirico
Phase One of Appsec Engineering: Awareness
Last week I published a post introducing three important phases of AppSec Engineering: Awareness, Enablement, and Enforcement. Over the next three posts I will dive into each of these topics to share best practices and guidelines you can roll out to optimize your security engineering practice. In my experience, the best AppSec programs start with AppSec awareness training. The goal is to provide your product team with enough information to know when they need security involvement. That’s a broad statement, so let’s break it down.This is part of a series
Read more >>
 Credit: Joe Basirico
Credit: Joe Basirico
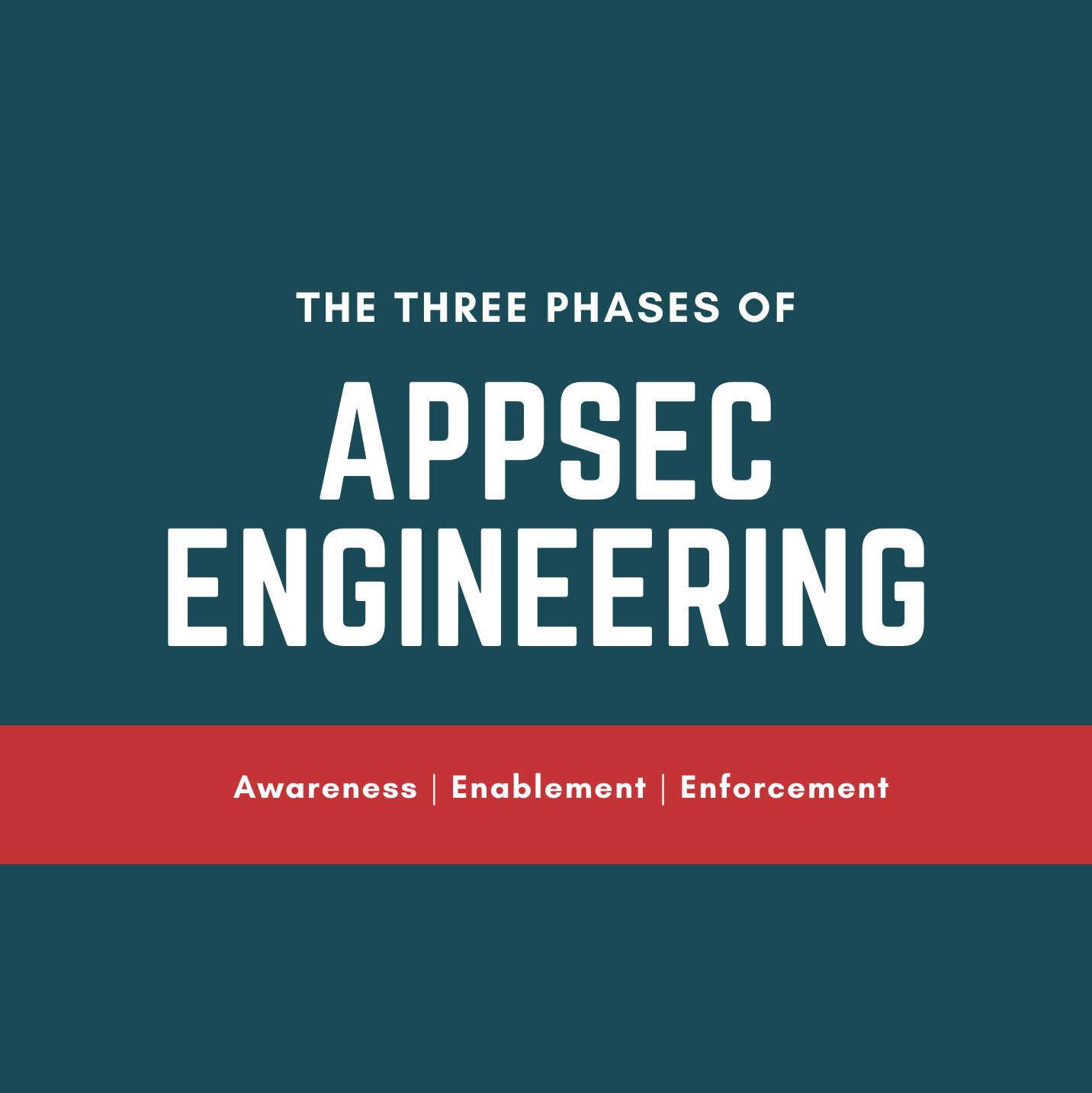
The Three Phases of Appsec Engineering
In order for an AppSec team to collaborate effectively with development teams they should think in three phases: Awareness, Enablement, and Enforcement. This month I’ll be dedicating an article to each. The focus of these articles will be on the critically important area of application security, focused on the roles involved in building software: developers (DevOps), testers, and architects.This is part of a series
Read more >>
 Credit: Joe Basirico & Rob Curran
Credit: Joe Basirico & Rob Curran
Building a Security Team of 500
I recently talked with a CISO friend of mine who was struggling to scale his security team. He has fewer than 10 security people on his team to support an organization with over 500 developers and 2000 employees. Responding to all of the requests which include: development best practices, legal and compliance, security awareness, IT security, trying to organize his team to perform the scanning, testing, reviews and more left him under water and stressed out!
Read more >>
 Credit: Pexels
Credit: Pexels
How to Scale an Application Security Program - Part Two
In my last blog post, I wrote about what an application security program is and why it matters. In this post, I’ll cover what it takes to build and scale an effective application security program. I’ve seen many different ways that a well-intentioned program can fail to meet its objectives. While there may be many ways to fail, there are just a few key characteristics that lead to success. The program must be:
Read more >>
 Credit: Pexels
Credit: Pexels
How to Scale an Application Security Program - Part One
In the late 1990s I worked on the security team for Internet Explorer. In fact, I was the first hire that Microsoft made in response to an influx of browser-based security vulnerabilities. I got to see what it looks like when a development team is bombarded by security problems that are serious enough to require a response and yet there’s no process to handle it. In the early days we would get at least one new vulnerability each week. The cost to respond was over one million dollars - per vulnerability! Every time it happened, we had to stop development, understand the problem, understand the fix, test the fix, and then release to customers. A team of over four hundred developers and testers was stopped in their tracks on a regular basis. You can only do that for so long before you realize that something has to change. On the Internet Explorer team we developed a new set of processes, skills, and tooling that allowed us to rise to the challenge. We did what we had to do to solve the problem while under a constant barrage of enemy fire. In the end, we built and scaled an application security program that worked not only for Internet Explorer but for the rest of Microsoft product development as well. Today that process is called the Microsoft SDL and Trustworthy Computing.
Read more >>
 Credit: Kroll Historical Maps
Credit: Kroll Historical Maps
A Traveler's Method of Learning Technology
My favorite thing about my career in security consulting has been the constant opportunity to learn new topics. Security weaves itself through every aspect of software, and software is everywhere. The phone in your pocket, the bluetooth chip in your headphones, your automobile, and the SCADA systems you rely upon every day execute millions of lines of code on your behalf. The idea that each of those systems gives me the opportunity to gain new knowledge is truly exciting. It can also be daunting when there is always so much to learn.
Read more >>
 Credit: Jay Heike @ Unsplash
Credit: Jay Heike @ Unsplash
Are You a Firefighter or a Building Inspector
Firefighters are heroes. They rush into burning buildings to save our families and heirlooms from disaster. They are there in the middle of the storm to help. Building Inspectors are bureaucrats. They tell us how to safely build and remodel while mitigating unforeseen threats that may never come. But who has saved more lives and property? It’s difficult to determine how many disasters have been averted by building codes or by the recommendations and requirements from building inspectors, but I suspect a lot more disasters are averted through their careful building plans, processes, and procedures than by firefighters responding to a fire.
Read more >>
 Credit: Dane Deaner on Unsplash
Credit: Dane Deaner on Unsplash
It's Always About People
It seems like everyone is struggling to build a scalable application security program these days. Budgets are small, internal politics and bureaucratic inertia are a real problem, and in the meantime the threat landscape isn’t waiting while your business figures things out. I would love it if my conversations with customers could be focused on a holistic, risk-centered approache that combines improvements to people, process, and tools in order to reduce risk to manageable levels.
Read more >>

Defense in Depth, What I Should Have Done to Save Myself From Dire Injury
I caught three of my fingers in a tablesaw this last weekend, which caused a severe hand injury, mangling my fingers, tearing off my fingernails, and breaking the bones. It was pretty terrible, but luckily the hand surgeon says I should have a complete recovery in a few months. Me being me, this got me thinking about some of the things that I could’ve done to mitigate the injury before it happened. It struck me that the threat modeling I was doing for my own physical safety, is analogous to a lot of the recommendations and guidance that I give companies for software security. In my case, my recommendations to myself boil down to the importance of focus while performing monotonous tasks, and the necessity for defense in depth.
Read more >>

Defcon - There Has Never Been a Better Time to Get Into Security
I just returned from the 27th Defcon security conference. I’ve been attending for the last 12 or so years and it has been interesting and fun to see the conference grow and mature. Once intimidating due to the homogenous attendees, lewd contests, and a “Try Harder” mantra, it has now evolved into a great place to learn and meet new people. Each year I speak at, or attend, a handful of security conferences. These range from the massive RSA Conference, where you can find hundreds of security vendors spending hundreds of thousand of dollars to hawk their latest security appliances, to small locally run, open source conferences that are run by engineers for engineers.
Read more >>

Can Security Training Change Lives?
I had the opportunity to spend a few days at a security conference last month, in which I talked with hundreds of people in the information security community about their fears, concerns, hopes, and plans. One thing that stood out to me was the sheer optimism and joy that most of the conference attendees brought with them. They were not there (only) for the swag or the cocktail hour or the chance to be away from their day jobs for a few days. The vast majority were there because they loved their jobs, believe in what they are doing, and wanted to learn more so they could bring that knowledge back to do their jobs even more effectively.
Read more >>